Red flags in a dating app: signs to be careful with
Some warning signs are obvious. Others disguise themselves as attention, romance, or the perfect conversation. This guide gathers the behavior patterns that research and real-life experience identify as risk signals in dating apps, with an interactive diagnostic tool to assess your situation.
1Why red flags in dating apps are different

Dating apps remove the social context that in real life acts as a natural filter. That makes certain warning signs harder to detect.
In a face-to-face interaction, we have body language, tone of voice, shared social context, and the ability to cross-check information with friends or mutual acquaintances. Dating apps remove most of those filters. What remains is a curated profile, a text conversation, and the information the other person decides to give you.
That does not make apps dangerous spaces by default, but it does make them spaces where certain warning signs become harder to detect because they are protected by anonymity, distance, and the ability to control one's personal narrative.
Stanford Social Innovation Review (2022): online dating environments have a significantly higher rate of exposure to manipulative behaviors than encounters in natural social settings, precisely because the cost of creating a false identity or using emotional manipulation techniques is almost zero. Anonymity reduces inhibition and the sense of responsibility.
FBI Internet Crime Complaint Center (IC3, 2024): romance scams generated losses of more than 1.1 billion dollars in the U.S. alone in 2023. The most common victim profile is not what many would expect: they are educated people with stable jobs and active social lives. The emotional sophistication of scams exceeds individual intuition.
Cialdini (2007) — Influence: The Psychology of Persuasion: the principles of reciprocity, scarcity, authority, and social proof are exactly the ones exploited by manipulative profiles on dating apps. Love bombing activates reciprocity. Artificial urgency activates scarcity. Knowing these mechanisms is the best protection.
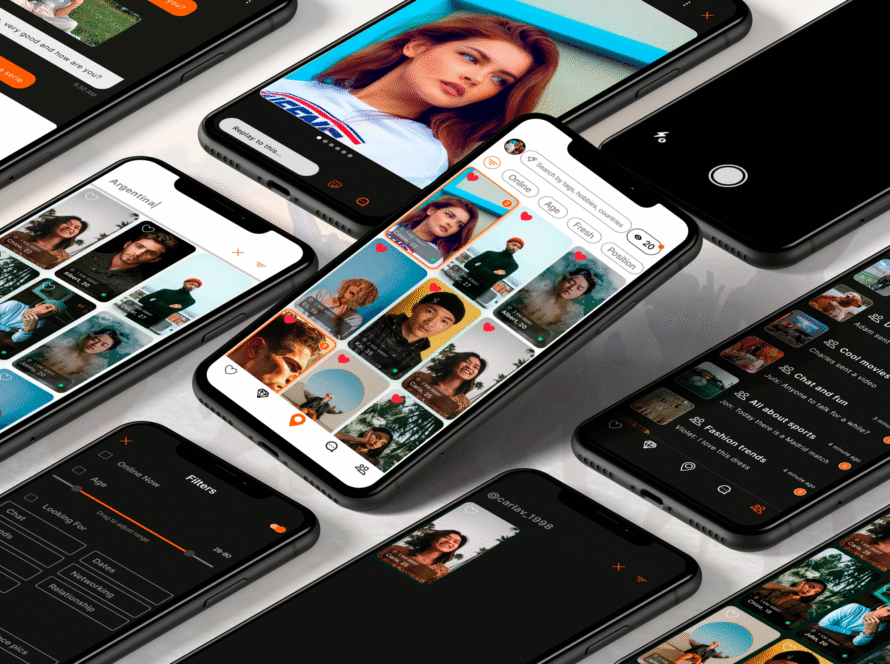
Xder — Community principles (2026): the platform identifies financial scams, sextortion, persistent harassment, and identity impersonation as grounds for immediate expulsion. Facial verification is available as a filtering tool for users who want to connect only with verified profiles.
"The problem is not that warning signs do not exist. The problem is that when we are emotionally invested, the brain reinterprets them as signs of intense interest."— Adapted from Cialdini (2007), on the principles of influence and reciprocity
2Red flags in the profile: signs before you even start talking
The profile is the first layer of information. And also the first opportunity to fabricate an identity. These are the warning signs that may appear before any conversation even begins.
There is only one profile photo, or all the photos look like they belong in a catalog: perfect lighting, ideal angles, no everyday context (friends, places, real-life moments).
🔍 Fake profiles use photos stolen from social media or generated by AI. A single professional-looking photo without personal context is a frequent catfishing pattern. On Xder, you can filter by users with facial verification to reduce this risk.
The bio seems written to appeal to everyone: "I love traveling, sports, enjoying life, and good food." No specificity, no real personality, no detail that only a real person would write.
🔍 Profiles generated by AI or used for scams tend toward maximum genericness to attract as many people as possible. Authentic specificity turns some people away; genericness attracts everyone. That is not accidental.
The geolocation shows one city but the profile says they "travel a lot" or are "just passing through." Or they appear in a city where it seems impossible for them to be, based on the context of their photos.
🔍 Geolocation-based apps like Xder show nearby profiles. If someone appears nearby but their story does not align with that context, it may be a profile using a VPN or manipulated geolocation.
They have no linked social media, do not show up in any basic search, or the networks they mention have very few posts and followers.
🔍 A real person in 2026 usually has some digital footprint. Complete absence is not privacy: it is constructed invisibility. It may be a sign of a profile recently created for specific purposes.
Doctor without Borders, offshore engineer, military abroad, international entrepreneur. Jobs that explain both frequent travel and limited availability, as well as the inability to meet in person.
🔍 These professions are the ones most commonly used in romance scams because they create credibility, justify physical absence, and build the scenario of an "exceptional person who for some reason is alone." The combination of these factors is an important warning sign.
The account was created very recently. There is no group history, little activity, no albums, and no accumulated content.
⚠️ On its own, it is not a critical sign: everyone was new at some point. But combined with other signals (generic profile, perfect photos, high-status profession), it raises the alert level.
3Red flags in the conversation: warning patterns in chat
Chat is where most warning signs become visible to those who know what to look for. These are the most common patterns and what they reveal about the other person's real intentions.
In the first message (or the first few exchanges), they ask to move to WhatsApp, Telegram, or any other platform outside the app. They may say that they "do not use the app much" or that "it is easier to talk there."
🔍 Moving the conversation off the app removes the safety mechanisms, report history, and the ability to block from within the platform. Scammers and abusive profiles want to operate outside the ecosystem where they can be reported. Xder's principles explicitly identify this as a risk signal.
When you ask specific questions (Where exactly do you work? What is the company called? What neighborhood do you live in?), they change the subject, give vague answers, or return the question without answering.
🔍 People with real profiles answer real questions without a problem. Systematically avoiding verifiable questions is the most reliable pattern of a false identity or hidden intent.
They tell you things that do not add up. They said they were an only child but later mention a sister. They said they lived in Madrid but then mention their office is in Barcelona. Small contradictions that accumulate.
🔍 Maintaining a false story for weeks is difficult. Inconsistencies are not always a sign of malice (they can also be simple slips), but when they are frequent and involve basic facts, they reflect a constructed narrative that is falling apart.
There is always a reason why they cannot video call: broken camera, bad connection, shyness, "I would rather meet in person." But the in-person meeting never happens either.
🔍 A video call is the most basic identity verification. Refusing one for more than one or two weeks without a verifiable reason is one of the clearest signs of catfishing or romance scam. Xder's safety guide explicitly recommends doing a video call if you have doubts.
You have been talking for weeks or months but they never make anything concrete happen. There is always something preventing it. The warmth of the conversation has no real-world counterpart in moving toward meeting.
🔍 It may be a romance scam (which needs time to build a bond before the "ask"), a breadcrumbing profile (seeking attention without commitment), or simply someone with no real intention of meeting. In any case, lack of progression is information.
The messages do not refer to what you have said. They are texts that could be sent to anyone. There is no personalization and no memory of previous conversations.
⚠️ It may be a bot, someone managing multiple conversations simultaneously with copy-paste, or simply someone with little interest. Personalization is the difference between real attention and noise.
🚩 Pressure to leave the app + evasion of specific questions + changing the subject = warning pattern
✅ Specific answers + reference to the profile + reciprocal questions = conversation with indicators of authenticity
4Emotional manipulation: love bombing, ghosting, and control cycles

Love bombing is an emotional control technique that begins as excessive attention

The idealization-devaluation cycle is one of the most common patterns in toxic relationships that begin online
Emotional manipulation in the context of dating apps has its own patterns. These are the most documented ones and the ones that create the most confusion because they are initially perceived as positive signals.
From the very first day: constant messages, intense declarations of affection too soon ("you're different from everyone I've ever met," "I feel like we've known each other for years"), elaborate future plans before you have even met.
🔍 Love bombing is a documented emotional control technique: it creates a debt of reciprocity (you received so much that you feel you should give something back), isolates you from others (because no one else gives that much attention), and establishes an artificial baseline of intensity that is later used as a lever of control.
They alternate between periods of intense attention and sudden disappearances or coldness without explanation. When they disappear and come back, the explanation is vague or blames you.
🔍 This pattern activates anxious attachment mechanisms: intermittent uncertainty generates more emotional dependence than consistent attention does (the principle of variable reinforcement, Skinner). It is one of the most frequent dynamics in emotionally abusive relationships.
They push for the relationship to move quickly: becoming exclusive very soon, meeting your family, making life plans together before meeting in person or after very few encounters.
🔍 Artificial urgency is one of Cialdini's influence principles: perceived scarcity ("if we do not move forward now, we will lose it") activates fear of loss more than desire for gain. Healthy relationships have their own rhythm, not the one an external person imposes.
There is always a crisis, a family problem, a difficult situation that requires your emotional attention. When you try to set a boundary, a new emergency appears.
🔍 Victimhood as a pattern (not as a temporary state) activates care and guilt, two of the most powerful mechanisms for keeping someone emotionally trapped. The difference between a person in genuine difficulty and this pattern is the frequency and the function it serves.
They disappear for days or weeks without warning and come back as if nothing happened. It may happen several times. Each return activates the hope that "this time it will be different."
🔍 The ghosting-and-return pattern (zombieing) may be breadcrumbing (keeping you as a backup option) or an indicator of disorganized attachment. In neither case is it a healthy foundation for building something real. Consistency is the minimum requirement for respect.
They make negative comments about your friends or family. They monopolize your time. They get upset when you spend time with other people. The relationship gradually takes up more and more space in your life.
🔍 Isolation is one of the most documented signs of a controlling dynamic. Healthy relationships coexist with both people's social environment; they do not compete with it. If someone pulls you away from your support network, that distancing also pulls you away from the people who could help you see the situation clearly.
5Romance scams and sextortion: the signs you should never ignore
Romance scams are the most serious end of the red-flag spectrum. They are not rare, they do not happen only to naïve people, and they are designed by professionals to overcome natural distrust. Understanding how they work is the only real protection.
Phase 1 — Building the bond (weeks or months): the fake profile establishes contact, seems attentive, remembers details, appears ideal. It creates trust and emotional dependence without any suspicious request. This phase can last a long time because the more emotionally invested the target becomes, the greater the likelihood they will pay when the moment arrives.
Phase 2 — The crisis: an urgent problem appears that requires money. Medical emergency. Trouble with an investment project that will supposedly generate returns. Need to pay for a flight to come see you. The first request is small, then gets bigger once the first payment is made.
Phase 3 — Escalation or disappearance: if you pay, the situation becomes more complicated and more money is needed. If you refuse, the person disappears or becomes aggressive. In cases of sextortion: they threaten to spread intimate images if you do not pay.
Why it works: there is no single victim profile. The emotional sophistication of these scams goes beyond individual intuition. The people who fall for them are normal people at a moment of real emotional vulnerability.
| Scam sign | How it appears | Level |
|---|---|---|
| First request for money (any amount, any reason) | Medical emergency, travel problem, "temporary" bank account issue, investment with guaranteed return. | Critical — Block and report |
| Mention of cryptocurrency or "low-risk" investments | "I have an investment system that has made me a lot of money, I can show you." Investment platforms that do not exist or are fraudulent. | Critical — Block and report |
| Request for intimate photos or videos before meeting | Trust is built gradually until intimate content is requested, which can then be used as extortion material. | Critical — Do not send |
| Threat to spread images (sextortion) | You already sent something and now they demand money not to leak it. They may be images captured from the screen without your knowledge. | Critical — Report to the platform and the police |
| Person with a job abroad who will soon "come see you" | The meeting never happens. There is always a problem preventing it: the flight, the visa, a last-minute emergency. | High — Active warning sign |
| Declarations of love very early + inability to meet | They feel something "very strong" but cannot meet. Classic combination of love bombing + obstacle to a real-life meeting. | High — Observe and verify |
🛡️ On Xder, facial verification reduces the risk of catfishing and fake profiles
Filter your search by facially verified users to make sure the person exists and matches their photos. Fewer fake profiles, more real connections.
Explore Xder →6Red flags on the first in-person date
If the online conversation passes the filter of the previous warning signs, the in-person meeting remains. Here too, there are specific signals worth knowing.
7Diagnostic tool: assess your situation
Check the signs you have observed in the person you are currently talking to. The result will give you guidance on the alert level of the situation.
Check only what you have observed in a real and concrete way, not what you imagine might happen.
8Frequently asked questions about red flags in dating apps
📚 Sources and references
- FBI Internet Crime Complaint Center (IC3). 2024 Internet Crime Report. Data on romance scams and economic losses.
- Cialdini, R.B. (2007). Influence: The Psychology of Persuasion. Harper Collins. Principles of reciprocity, scarcity, and social proof applied to manipulation.
- Skinner, B.F. (1938/1974). The Behavior of Organisms and About Behaviorism. On intermittent variable reinforcement and the dependence it generates.
- Dutton, D.G. & Goodman, L.A. (2005). Coercion in intimate partner violence: Toward a new conceptualization. Sex Roles, 52(11–12). On the cycle of emotional control.
- Stanford Social Innovation Review (2022). Vulnerability and manipulation in digital dating environments.
- Xder — Community principles and safety guide (2026). Zero-tolerance rules and scam response protocol.
- Xder — About Xder: facial verification and safety filters.
- Tinder Safety Center / Match Group Safety Report (2023). Statistics on abusive behavior in dating apps.
Red flags do not always scream. Many of the most serious ones arrive disguised as attention, romantic intensity, or emotional urgency. Knowing the patterns does not make online dating something dangerous: it makes it something you can navigate with more information and less risk.
Critical signs — requests for money, systematic refusal of video calls, identity evasion, sextortion — have no context that justifies them. Act on them regardless of how much time you have already invested. High- or medium-level signs should be assessed as a pattern: one may have an explanation; five do not.
And if something simply feels off even if you cannot articulate exactly why, take it seriously. Intuition processes real information. On Xder, facial verification, the reporting system, and active moderation exist so that the connections you build are real and safe. Xder →